Supply Chain Attack: Difference between revisions
No edit summary |
No edit summary |
||
| Line 1: | Line 1: | ||
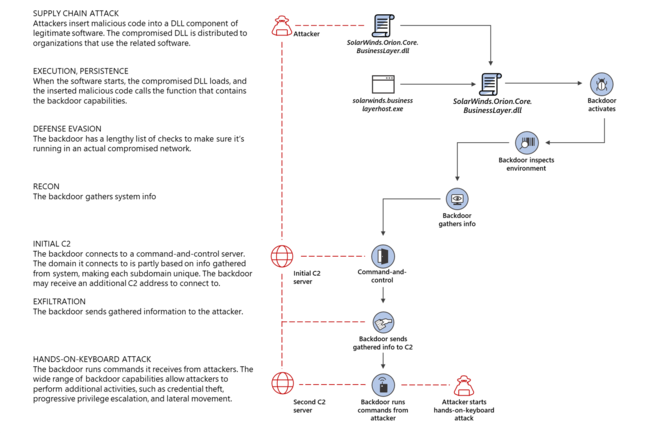
[[FIle:Fig1-Solorigate-attack-chain.png|650px|right|thumbnail|Solorigate malware infection chain ([https://www.microsoft.com/security/blog/2020/12/18/analyzing-solorigate-the-compromised-dll-file-that-started-a-sophisticated-cyberattack-and-how-microsoft-defender-helps-protect/ Flowchart from Microsoft Security blog])]] A '''Supply Chain Attack''' is when a threat actor makes use of unsecured network protocols, unprotected server infrastructures, or unsafe coding practices. The supply chain attacker breaks in, changes source codes, and hides malware in build and update processes.<ref>[https://docs.microsoft.com/en-us/windows/security/threat-protection/intelligence/supply-chain-malware Supply Chain Malware, Microsoft]</ref> | [[FIle:Fig1-Solorigate-attack-chain.png|650px|right|thumbnail|Solorigate malware infection chain ([https://www.microsoft.com/security/blog/2020/12/18/analyzing-solorigate-the-compromised-dll-file-that-started-a-sophisticated-cyberattack-and-how-microsoft-defender-helps-protect/ Flowchart from Microsoft Security blog])]] A '''Supply Chain Attack''' is when a threat actor makes use of unsecured network protocols, unprotected server infrastructures, or unsafe coding practices. The supply chain attacker breaks in, changes source codes, and hides malware in build and update processes.<ref>[https://docs.microsoft.com/en-us/windows/security/threat-protection/intelligence/supply-chain-malware Supply Chain Malware, Microsoft]</ref> | ||
==Recent Attacks== | |||
Recently, criminals have targeted the following software vendors and IT services companies to infect their clients: | |||
* '''Kaseya''' <br/> | |||
On July 2, hackers breached this Florida-based IT management software company. Kaseya specializes in monitoring and controlling the computer networks of “managed service providers” that sell their IT and cybersecurity services to hundreds of thousands of small- and medium-sized businesses. After the hackers infected 50 of Kaseya's managed service providers, they were able to enter the systems of those companies' 1,500 clients. The hackers encrypted the victims’ data and demanded US$50 million in exchange for the key.<ref>[https://qz.com/2030053/what-is-a-supply-chain-cyber-attack/ What is a supply chain attack, Quartz]</ref> | |||
==References== | ==References== | ||
Revision as of 11:40, 26 July 2021
A Supply Chain Attack is when a threat actor makes use of unsecured network protocols, unprotected server infrastructures, or unsafe coding practices. The supply chain attacker breaks in, changes source codes, and hides malware in build and update processes.[1]
Recent Attacks
Recently, criminals have targeted the following software vendors and IT services companies to infect their clients:
- Kaseya
On July 2, hackers breached this Florida-based IT management software company. Kaseya specializes in monitoring and controlling the computer networks of “managed service providers” that sell their IT and cybersecurity services to hundreds of thousands of small- and medium-sized businesses. After the hackers infected 50 of Kaseya's managed service providers, they were able to enter the systems of those companies' 1,500 clients. The hackers encrypted the victims’ data and demanded US$50 million in exchange for the key.[2]
