Cybersecurity: Difference between revisions
No edit summary |
|||
| Line 1: | Line 1: | ||
'''Cybersecurity''' is the practice of protecting systems, networks, and programs from digital attacks. Cyberattacks usually seek to access, change, or destroy sensitive information; extort money from their victims; or disrupt business as usual. [https://www.cisco.com/c/en/us/products/security/what-is-cybersecurity.html#~types-of-threats What is Cybersecurity, Cisco] Implementing cybersecurity measures is challenging because it is a cat-and-mouse game, and today there are more devices than people. | '''Cybersecurity''' is the practice of protecting systems, networks, and programs from digital attacks. Cyberattacks usually seek to access, change, or destroy sensitive information; extort money from their victims; or disrupt business as usual.<ref>[https://www.cisco.com/c/en/us/products/security/what-is-cybersecurity.html#~types-of-threats What is Cybersecurity, Cisco]</ref> Implementing cybersecurity measures is challenging because it is a cat-and-mouse game, and today there are more devices than people. | ||
Ensuring the cybersecurity of computers, networks, programs, and data relies on multiple layers of protection involving the detection, investigation, and remediation of threats. Users need to understand and comply with basic data security principles like choosing strong passwords, being wary of attachments in email, and backing up data. However, many questions remain over whether people can outsmart [[Social Engineering Attacks]]. Common technology used to protect endpoint devices, such as computers, smart devices, and routers; networks; and the cloud, include firewalls, DNS filtering, malware protection, antivirus software, and email security. | Ensuring the cybersecurity of computers, networks, programs, and data relies on multiple layers of protection involving the detection, investigation, and remediation of threats. Users need to understand and comply with basic data security principles like choosing strong passwords, being wary of attachments in email, and backing up data. However, many questions remain over whether people can outsmart [[Social Engineering Attacks]]. Common technology used to protect endpoint devices, such as computers, smart devices, and routers; networks; and the cloud, include firewalls, DNS filtering, malware protection, antivirus software, and email security. | ||
| Line 8: | Line 8: | ||
==Government Involvement== | ==Government Involvement== | ||
Government leaders have different understandings and expectations of how involved a government should be in a nation’s cybersecurity. | Government leaders have different understandings and expectations of how involved a government should be in a nation’s cybersecurity. | ||
McKinsey suggests considering several questions to ascertain a government’s role in cybersecurity. [https://www.mckinsey.com/industries/public-and-social-sector/our-insights/asking-the-right-questions-to-define-governments-role-in-cybersecurity#] | McKinsey suggests considering several questions to ascertain a government’s role in cybersecurity.<ref>[https://www.mckinsey.com/industries/public-and-social-sector/our-insights/asking-the-right-questions-to-define-governments-role-in-cybersecurity# Defining Govts' Role in Cybersecurity, McKinsey]</ref> | ||
# Who is accountable? | # Who is accountable? | ||
#*Some national and state governments have consolidated accountabilities into a clear structure, such as Estonia’s Cyber Security Council, or have crisis-response mechanisms as in Sweden. | #*Some national and state governments have consolidated accountabilities into a clear structure, such as Estonia’s Cyber Security Council, or have crisis-response mechanisms as in Sweden. | ||
| Line 24: | Line 24: | ||
==The Industry== | ==The Industry== | ||
===Providers=== | ===Providers=== | ||
[[File:Billion-dollar cybersecurity exits, CB Insights.png|655px|right|(CB Insights)]]In the past decade, two dozen cybersecurity startups have attained IPO or M&A values of $1 billion; 10 of them since 2017. [https://www.cbinsights.com/research/cybersecurity-billion-dollar-exits-infographic/ ] | [[File:Billion-dollar cybersecurity exits, CB Insights.png|655px|right|(CB Insights)]]In the past decade, two dozen cybersecurity startups have attained IPO or M&A values of $1 billion; 10 of them since 2017.<ref>[https://www.cbinsights.com/research/cybersecurity-billion-dollar-exits-infographic/ Cybersecurity Exits, CB Insights]</ref> | ||
===Clients=== | ===Clients=== | ||
PwC conducted a survey in | PwC conducted a survey in 2020 and released it as “Global Digital Trust Insights 2021.” They asked 3,249 business and technology executives about their CISOs and the present and future of cybersecurity.<ref>[https://www.pwc.com/us/en/services/consulting/cybersecurity/library/assets/pwc-2021-global-digital-trust-insights.pdf Trust Insights, PwC]</ref> Some of their findings included: | ||
*Nearly all (96%) say | *Nearly all (96%) say they would adjust their cybersecurity strategy due to COVID-19. | ||
*Half are more likely now to consider cybersecurity in every business decision, up from 25% in 2019. | *Half are more likely now to consider cybersecurity in every business decision, up from 25% in 2019. | ||
*More (55%) are increasing cyber budgets than decreasing them in 2021. | *More (55%) are increasing cyber budgets than decreasing them in 2021. | ||
*However, most executives lack confidence that their cybersecurity budgets align with the most significant risks. | |||
Revision as of 17:18, 14 May 2021
Cybersecurity is the practice of protecting systems, networks, and programs from digital attacks. Cyberattacks usually seek to access, change, or destroy sensitive information; extort money from their victims; or disrupt business as usual.[1] Implementing cybersecurity measures is challenging because it is a cat-and-mouse game, and today there are more devices than people.
Ensuring the cybersecurity of computers, networks, programs, and data relies on multiple layers of protection involving the detection, investigation, and remediation of threats. Users need to understand and comply with basic data security principles like choosing strong passwords, being wary of attachments in email, and backing up data. However, many questions remain over whether people can outsmart Social Engineering Attacks. Common technology used to protect endpoint devices, such as computers, smart devices, and routers; networks; and the cloud, include firewalls, DNS filtering, malware protection, antivirus software, and email security.
History
- The Massachusetts Institute of Technology was granted the first US patent for a cryptographic communication system in 1983.
Government Involvement
Government leaders have different understandings and expectations of how involved a government should be in a nation’s cybersecurity. McKinsey suggests considering several questions to ascertain a government’s role in cybersecurity.[2]
- Who is accountable?
- Some national and state governments have consolidated accountabilities into a clear structure, such as Estonia’s Cyber Security Council, or have crisis-response mechanisms as in Sweden.
- Germany has its Bundesamt für Sicherheit in der Informationstechnik (Federal Office for Information Security).
- The United Kingdom’s National Cyber Security Centre (NCSC) has been cited as a model for government-level cybersecurity.
- How centralized is it?
- Japan’s Cyber Security Strategic Headquarters hosts audit and regulation functions in a centralized agency as does Romania’s Association for Information Security Assurance.
- India has dispersed audit functions across multiple bodies.
- Australia introduced a notifiable-data-breaches scheme in 2017, making it a legal requirement to notify affected individuals and the Office of the Australian Information Commissioner of serious data breaches.
- Relationship with the private and academic sectors?
- Singapore’s National Cybersecurity R&D Programme supports public–private research partnerships and budgeted $190 million Singapore dollars ($137.85 million) in the national strategy for the creation of the National Cybersecurity R&D Laboratory at the National University of Singapore.
- How does it define national critical infrastructure?
- In the United States, the Department of Homeland Security coordinates a national infrastructure-protection plan and requires sector-specific agencies, such as the Cybersecurity and Infrastructure Security Agency (CISA) to develop sector-specific plans.
The Industry
Providers
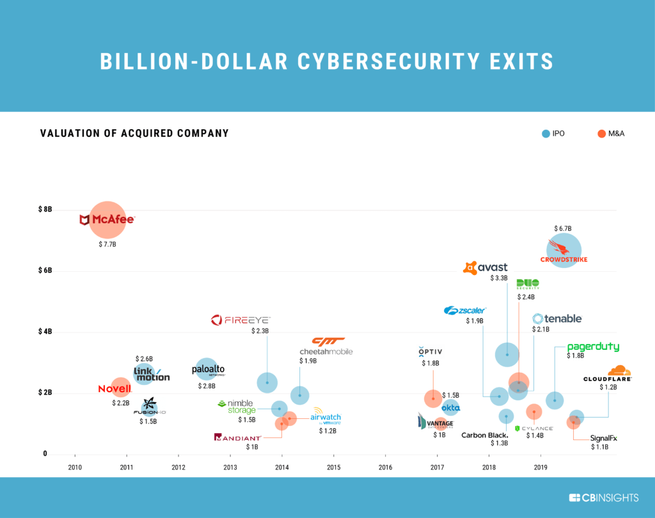
In the past decade, two dozen cybersecurity startups have attained IPO or M&A values of $1 billion; 10 of them since 2017.[3]
Clients
PwC conducted a survey in 2020 and released it as “Global Digital Trust Insights 2021.” They asked 3,249 business and technology executives about their CISOs and the present and future of cybersecurity.[4] Some of their findings included:
- Nearly all (96%) say they would adjust their cybersecurity strategy due to COVID-19.
- Half are more likely now to consider cybersecurity in every business decision, up from 25% in 2019.
- More (55%) are increasing cyber budgets than decreasing them in 2021.
- However, most executives lack confidence that their cybersecurity budgets align with the most significant risks.
