Ransomware
Ransomware is a form of malware designed to encrypt files on a device, rendering any files and the systems that rely on them unusable. Malicious actors then demand ransom in exchange for decryption. They threaten to sell or leak exfiltrated data or authentication information if the ransom is not paid.
RaaS is a subscription for ransomware tools. RaaS allows cybercrime groups to extend their reach and decentralizes attacks, complicating efforts to disrupt them. The RaaS creators take a percentage of each successful ransom payment.[1]
Recent Statistics and History-Making Events
- Average downtime due to ransomware: 21 days[2]
- Average recovery time for organizations: 287 days[3]
- Total victims paid to decrypt their data: US$350 million[4]
- Change in payout from 2019 to 2020: 311% increase[5]
- Total victims paid to decrypt their data: US$350 million[6]
- Average individual payment: US$312,493[7]
- Year-over-year difference from 2019: 171% increase [8]
- Number of U.S.-based governments, healthcare facilities, and schools attacked: 2,400[9]
- The critical infrastructure sector that experienced more ransomware attacks than any other industry: Healthcare[10]
- On September 10, 2020, ransomware contributed to the first reported death related to a cyber attack, after an emergent patient had to be re-directed from a ransomware victim hospital in Germany.[11]
- On April 29, 2021, DHS Secretary Alejandro Mayorkas declared ransomware a national security threat.[12]
Mitigation
- CISA's StopRansomware.gov recommends that individual users:
- Update software and operating systems with the latest patches, because hackers most commonly attack outdated applications and operating systems;
- Never click on links or open attachments in unsolicited emails;
- Constantly back up data, keep it on a separate device, and store it offline;
- Use strong passwords; and
- Only connect to secure networks, use a VPN, and make sure you have a firewall.[13]
- Recommendations for organizations include:
- Heavily restrict user permissions to install and run software applications;
- Enable the strongest spam filters possible; and
- Configure firewalls to block access to known malicious IP Addresses.[14]
- On April 29, 2021, the Institute for Security and Technology launched the Ransomware Task Force (RTF), which released a comprehensive framework outlining 48 actions and their timelines for governments and industry leaders to undertake to disrupt the ransomware business model and mitigate attacks' impacts.[15]
- Alternatives to payment include:
- working with the No More Ransom Project, which helps victims decrypt data without paying attackers;
- working with law enforcement, such as the FBI, immediately after noticing the attack
- To manage the fallout, an industry has grown up around cyberattack recovery. Cyber insurance (aka cybersecurity insurance, cyber risk insurance, data breach insurance, or cyber liability insurance) protects against some of the financial and legal consequences of cyber risks and attacks. This industry is focused on mitigating the side effects of cyber attacks and data breaches.[16] The backstop support of insurance may encourage ransomware attackers, as insured victims may be more likely to pay.[17] However, insurance providers generally require that clients adhere to baseline security practices, connect victims to recovery experts and law enforcement, and leverage market tools to incentivize security standards and discourage organizations from paying ransom.[18]
- Zero Trust architecture limits lateral movement and contains the blast radius or ransomware attacks.[19]
Debates
To Pay or Not to Pay?
The "DON'T make it an option" Camp
- On June 10, 2021, FBI Director Christopher Wray testified before Congress that companies should not pay the ransom because doing so encourages more of this kind of activity and that victims may pay the ransom but not get their systems back.[20]
- U.S. Energy Secretary Jennifer Granholm supports legislation banning ransomware payments.[21]
- The Biden administration formed a multi-agency task force working on freeze ransomware payments made through cryptocurrency platforms[22]
- New York introduced and North Carolina passed bills to prohibit municipal ransomware payments.[23][24]
The "Maybe DO let it remain an option" Camp
- Bryan Hornung, the founder of cybersecurity firm Xact IT Solutions, argued that if companies cannot pay ransoms, they will have to close their doors and lawsuits will proliferate; also, the attackers may seek to extort individuals whose data are compromised if organizations do not pay.
- Ed Cabrera, CCO at Trend Micro, said that criminalizing ransom payments will lead hackers to make more lethal attacks and increase the pain.[25]
- In the Harvard Business Review, Rahul Telang opined that in attacking companies rather than consumers, ransomware is forcing organizations to pay a steep, direct price for lax security and ultimately focusing organizations' attention on improving their cybersecurity and protecting their networks.[26]
- Coveware's core business model is negotiating ransomware sums.[27]
Notorious Cases
Cobalt Strike
Cobalt Strike is the legitimate, commercially available tool used by network penetration testers that has been co-opted by threat actors.[28] It is also known as Agentemis, BEACON, and CobaltStrike, and the threat actors that have used it include APT 29, APT32, APT41, Anunak, Cobalt, Codoso, CopyKittens, DarkHydrus, FIN6, Leviathan, Mustang Panda, Shell Crew, Stone Panda, UNC1878, UNC2452, and Winnti Umbrella.[29]
Maze Cartel
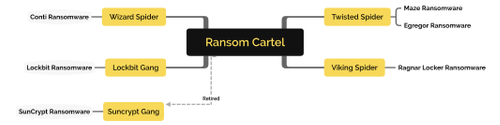
In June 2020, the Maze Cartel publicly announced that TWISTED SPIDER, VIKING SPIDER, and LockBite were running a collaborative business arrangement.[30] In November 2020, Twisted Spider announced they were shutting down the cartel operations.[31]
The people who comprise the cartel originate from eastern Europe, primarily speak Russian, and ensure that their payloads do not execute on Russian victims. Twisted Spider used Maze ransomware from May 2019 to November 2020 and Egregor beginning in September 2020, each using its own malware, infrastructure, and online personas. The operators are very communicative with media, cybersecurity firms, and other cybercriminals.[32] Viking Spider began its ransom operations in December 2019. Wizard Spider has multiple teams and has been participating in attacks since 2016. The Lockbit Gang was the first to automate attacks. SunCrypt was the first gang to introduce denial of service attacks to extort victims.[33]
Darkside
Darkside is a group of hackers that carried out a significant ransomware attack in May 2021. In August 2020, Darkside introduced its Ransomware-as-a-Service (RaaS) in a press release. The group provides web chat support to victims, builds intricate data leak storage systems with redundancy, and performs financial analysis of victims prior to attacking. The group is suspected to be former IT security professionals and is known to have a code of conduct that includes not attacking hospitals, schools, non-profits, or governments, but rather big organizations. After the May 2021 Colonial Pipeline attack, Varonis’s reverse engineering revealed that Darkside’s malware checked device language settings to ensure that they don’t attack Russia-based organizations.[34] Darkside has Windows and Linux toolsets and is similar to NetWalker and REvil in that it has an affiliate program that offers anyone who helps spread their malware 10-25% of the payout.
Darkside
- runs command and control over TOR,
- avoids nodes where EDR is running,
- uses waiting periods,
- saves noisier actions for later stages,
- customizes code and connection hosts for each victim,
- obfuscates with encoding and dynamic library loading, and
- performs anti-forensics techniques, such as deleting log files.
TrickBot
TrickBot is ransomware that was first identified in 2016. It is a trojan developed and operated by a group of hackers who initially made it as a banking trojan to steal financial data. TrickBot has become a highly modular, multi-stage suite of tools to conduct myriad illegal cyber activities.[35] TrickBot has been used
- To exfiltrate data (email, credentials, point-of-sale info);
- For crypto-mining; and
- For host enumeration (reconnaissance of Unified Extensible Firmware Interface (UEFI) or Basic Input/Output System (BIOS) firmware)
Operators include:
Relies on:
- Emotet and Bokbot
- Spearphishing, spam campaigns, malvertising, and network vulnerabilities, such as Server Message Block, to gain initial access
Microsoft Disrupts Trickbot
On October 12, 2020, Microsoft announced that it had disrupted Trickbot following a court order from the United States District Court for the Eastern District of Virginia, which granted Microsoft's request to halt Trickbot’s operations. Microsoft identified and disabled the infrastructure Trickbot used to communicate with and control victim computers, how infected computers talked with each other, and how Trickbot evaded detection and disruption previously. The corporation also identified the servers' IP addresses of servers.[40]
Netwalker
In 2019, Netwalker was sent out into the world from the cybercrime group Circus Spider, who allowed hackers to rent access to their code in exchange for a percentage of the funds received.[41]
Conti
Conti ransomware uses a double-extortion technique. Attackers send a phishing email originating from an address that the victim trusts.[42]
REvil
Aka Sodin aka Sodinokibi, REvil has a reputation for extorting larger ransom payments than their competitors and promoting cybercrime forums.[43] The FBI accused REvil of orchestrating a ransomware attack on the world's largest meat processing company, JBS, in June 2021. JBS paid US$11 million in ransom to decrypt their files.[44]
REvil Suddenly Goes Offline
On July 13, 2021, Monitors discovered that a payment website and a blog run by the REvil group suddenly became unreachable, leading many to speculate that U.S. or Russian officials may be behind the disappearance.[45]
Ryuk
From 2018 to 2020, Ryuk spread via malicious (phishing) emails with links and attachments, notoriously attacking EMCOR Group and Epiq Global.
SamSam
From 2015 to 2018, SamSam infected the municipal/state services of Atlanta, Colorado, and San Diego and 200 public institutions/organizations.[46]
CryptoLocker
In 2013, a new type of ransomware, also known as Gameover Zeus, used the advent of Bitcoin transactions and the latest in encryption, using 2048-bit RSA key pairs generated from a command-and-control server. Only computers running a version of Windows are susceptible to Cryptolocker (it does not target Macs).[47]
AIDS Trojan
In 1989, one of the first ransomware attacks ever documented, also known as the PC Cyborg Virus, was released via floppy disk. Victims sent US$189 to a P.O. box in Panama to restore access to their systems.[48]
References
- ↑ Ransomware Stats 2021, Varonis blog
- ↑ Ransomware Payments Fall as Fewer Companies Pay Data Exfiltration Extortion Demands, Feb 1, 2021
- ↑ The State of Ransomware in the US: Report and Statistics 2020, Emisoft Blog, Jan 18, 2021
- ↑ 2021 Crypto Crime Report
- ↑ 2021 Crypto Crime Report
- ↑ 2021 Crypto Crime Report
- ↑ Ransomware Threat Assessments, Unit 42, Palo Alto Networks March 17, 2021
- ↑ Ransomware Threat Assessments, Unit 42, Palo Alto Networks March 17, 2021
- ↑ RTF Report 2021, pg. 7
- ↑ 2021 Cyber Security Stats, PurpleSec
- ↑ First Death from Ransomware, ZDNet
- ↑ Breaking Defense
- ↑ CISA Tips
- ↑ Ransomware FAQs, CISA
- ↑ RTF, IST
- ↑ Cyber insurance, Zeguro
- ↑ Extortion Economy, ProPublica
- ↑ RTF Report, IST, pg 13
- ↑ Adopting zero trust architecture can limit ransomware’s damage, VentureBeat
- ↑ FIB Director testifies, CSPAN
- ↑ Granholm on Meet the Press, NBC News
- ↑ White House Cybersecurity Task Force, CBS News
- ↑ 2019 NY Senate Bills
- ↑ 2021 NC Senate Bills
- ↑ Banning Ransomware payments could lead to new crises, Forbes
- ↑ Could Ransomware Attacks Ultimately Benefit Consumers? HBR, August 02, 2021
- ↑ Q2 Ransom Payments Decline, Coveware
- ↑ Cobalt Strike Usage Explodes Among Cybercrooks
- ↑ Cobalt Strike, Malpedia
- ↑ History of Ransomware, CrowdStrike
- ↑ The rise and fall of Maze Cartel, ChaslesCorp
- ↑ Ransom Mafia, Analyst1
- ↑ Ransom Mafia, Analyst1
- ↑ Analysis of Darkside, Varonis Blog
- ↑ CISA TrickBot Fact Sheet
- ↑ Wizard Spider, Crowdstrike
- ↑ WS sharing the same web, Crowdstrike
- ↑ WS Adversary, Crowdstrike
- ↑ Gold Blackburn, Secureworks
- ↑ New action to combat ransomware ahead of U.S. elections, Microsoft
- ↑ 2021 Ransomware Stats, Varonis blog
- ↑ 2021 Ransomware Stats, Varonis blog
- ↑ 2021 Ransomware Stats, Varonis blog
- ↑ REvil behind JBS attack
- ↑ REvil: Ransomware gang websites disappear from the internet, BBC
- ↑ Real and Famous Ransomware Cases, Gatefy
- ↑ Cryptolocker, Kaspersky
- ↑ History of Ransomware, CrowdStrike
ICANNWiki resources: Special Pages | Content Guide | Documentation | Development || Maintenance: Articles needing attention | Candidates for deletion || Projects: Internet & Digital Governance Library
